Learning Paths
Last Updated: March 31, 2026 at 12:30
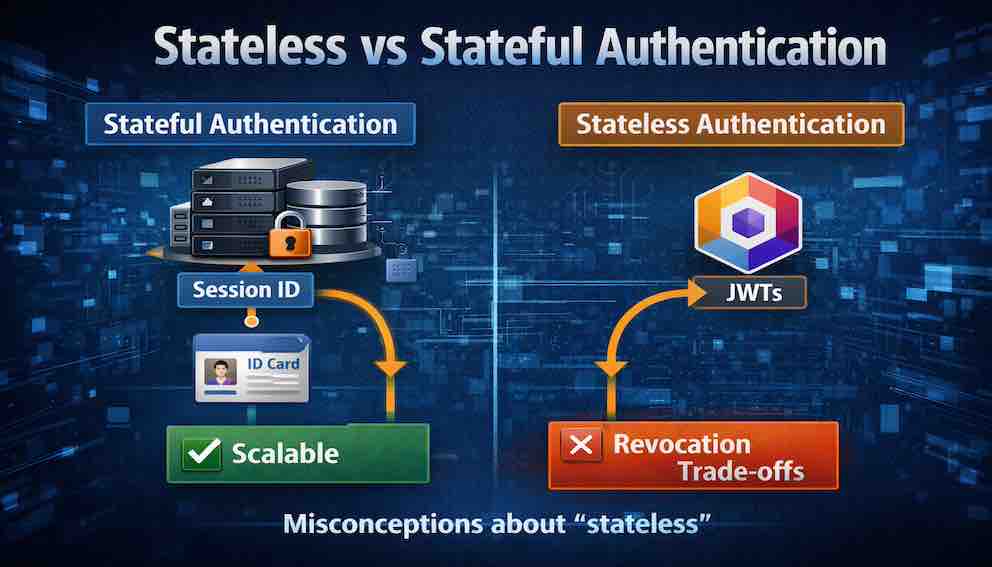
Stateless vs Stateful Authentication
Sessions vs JWTs, scaling vs revocation trade-offs, and why "stateless" is often misunderstood
The choice between stateful sessions and stateless JWTs is one of the most consequential decisions in authentication design. Stateful sessions give you immediate revocation and fine-grained control at the cost of a shared session store, while stateless JWTs give you effortless horizontal scaling at the cost of making logout and revocation genuinely difficult. This article walks through the complete trade-off matrix, debunks common misconceptions about what "stateless" actually means, and presents three hybrid patterns that give you the best of both worlds. By the end, you'll know exactly when to use sessions, when to use JWTs, and how to avoid the $2 million mistake of choosing the wrong one
The $2 Million Mistake
Consider a fast-growing SaaS company that built authentication around JSON Web Tokens. The reasoning was sound on its face: JWTs are stateless, they scale horizontally, and sessions require shared storage. For a team expecting rapid growth, that seemed like the right foundation.
At 50,000 users, the system worked fine. At 500,000, still fine. Then the company launched a feature requiring real-time permission changes — managers revoking a team member's access instantly. Suddenly, the stateless architecture created a serious problem. A revoked user could still access the system for up to 24 hours — the JWT's full expiration window.
The company had two choices: shorten the expiration to minutes (forcing users to log in constantly) or build a revocation blacklist (storing state anyway — the very thing they'd moved to JWTs to avoid). They chose a third option: rewrite the entire authentication system using server-side sessions. The rewrite took six months and cost over $2 million in engineering time.
The original decision wasn't reckless — it was a reasonable call made fully understanding the trade-off. JWTs genuinely do offer scaling advantages. The problem was that those advantages came with a constraint — limited revocation — that only became critical later, when product requirements changed.
That is the nature of this particular trade-off, and it's exactly what this article is here to unpack.
Part One: The Core Distinction
Here is the simplest way to understand the difference:
Stateful authentication (sessions): The server stores a record of the session. The client holds only a random identifier — a session ID. When the client makes a request, the server looks up the session record to determine who the user is.
Stateless authentication (tokens like JWTs): The server stores nothing. The client holds a self-contained token that contains the user's identity and claims. When the client makes a request, the server verifies the token's signature and extracts the identity directly from the token.
Here is the trade-off in a single sentence:
Stateful sessions give you control and revocation at the cost of scalability. Stateless tokens give you scalability at the cost of control and revocation.
There is no right answer for every system. There is only the right answer for your system.
Part Two: Stateful Authentication (Sessions)
How It Works
When a user logs in to a stateful system:
- The server verifies the user's credentials (password, MFA, etc.)
- The server generates a random, unguessable session ID — for example,
s:7f8e9d0c1b2a3f4e5d6c7b8a9f0e1d2c - The server stores a session record in a session store (database, Redis, or in-memory cache) containing the user ID, session creation time, expiration time, and any additional claims such as role, permissions, or IP address
- The server sends the session ID to the client as a cookie
- On every subsequent request, the client sends the session ID back, the server looks up the session record, validates it hasn't expired, and attaches the user identity to the request
The session ID itself contains no information about the user. It's a random string. All the information lives on the server.
The Session Store
The session store is the heart of stateful authentication. Common options include:
In-memory (process memory) is the fastest option but data is lost on restart and it only works for a single server. This is suitable for development or tiny applications.
Database (PostgreSQL, MySQL) is slower but persistent and can be helped by read replicas. Appropriate for small to medium applications.
Redis or Memcached is very fast, optionally persistent (Redis can persist), and distributes well under high load. This is the right choice for most production applications.
Distributed cache (ElastiCache, etc.) offers fast, horizontally scalable, configurable persistence — ideal for large-scale applications.
The hidden cost: every authenticated request requires at least one round trip to the session store. At scale, your session store must handle thousands or millions of lookups per second.
Advantages of Stateful Sessions
Immediate revocation. When a user logs out, you delete the session record. When an admin suspends an account, you delete all session records for that user. The moment the record is gone, the session ID becomes worthless. No waiting for a token to expire.
Fine-grained session control. You can see all active sessions for a user, terminate specific sessions ("log out of all other devices"), and track metadata such as IP address, user agent, and last activity time.
No sensitive data on the client. The session ID is a random string. If stolen, the attacker only gains access for as long as the session lives — and you can revoke it immediately upon detection.
Simple token format. Session IDs are just random strings. There is no complex signature verification, no algorithm confusion vulnerabilities, no parsing bugs.
Disadvantages of Stateful Sessions
Not suited to stateless API calls. REST APIs are designed around the principle that each request is self-contained and carries everything the server needs to process it. Session IDs break that contract — they require the server to reach out to an external store to reconstruct context for every request. This matters in practice when building APIs consumed by third parties, microservices communicating with each other, or any integration where the client cannot be expected to manage cookies. In those contexts, a session-based approach introduces a hidden dependency that the API consumer has no visibility into and no control over.
Scalability requires shared storage. You cannot simply add more server instances without ensuring every instance can reach the same session store. That store becomes a centralized dependency.
Performance cost per request. Every authenticated request requires a lookup. At very high scale — hundreds of thousands of requests per second — even Redis can become a bottleneck.
Session store is a single point of failure. If your Redis instance goes down and is not clustered, all authenticated requests fail. Users are effectively logged out until the store recovers.
Harder to implement across domains. Cookies are domain-specific. If you have multiple domains (app.example.com, api.example.net), sharing a session cookie is complex.
Mobile and native apps require extra work. Mobile apps don't handle cookies as seamlessly as browsers. You often end up storing the session ID in local storage and sending it in the Authorization header manually.
When to Choose Stateful Sessions
Choose stateful sessions when you need immediate revocation — in banking, healthcare, or enterprise SaaS. When you need fine-grained session visibility. When your scale is moderate (thousands to low millions of active sessions). When you're building a traditional web application. Or simply when you want to minimise client-side complexity.
Part Three: Stateless Authentication (JWTs)
How It Works
When a user logs in to a stateless system:
- The server verifies the user's credentials
- The server creates a JWT containing a header (algorithm and token type), a payload (claims like user ID, role, expiration time), and a signature (cryptographic proof that the token hasn't been tampered with)
- The server sends the JWT to the client — in a cookie, response body, or as a Bearer token
- The client stores the JWT (in
localStorage,sessionStorage, or a cookie) - On every subsequent request, the client sends the JWT in the
Authorization: Bearer <token>header - The server validates the signature, checks expiration, and extracts the user identity from the payload
The server stores nothing. All the information needed to authenticate the user is embedded in the token itself.
The JWT Structure
A JWT looks like this:
Three parts, separated by dots.
The header declares the algorithm used to sign the token — for example, HS256. The payload contains the actual claims: user ID, expiration time, role, and any custom data the server chose to include. Both are simply base64-encoded, which means anyone holding the token can decode and read them. There is no encryption here. A JWT is not a secret — it is a signed statement.
The signature is what makes the token trustworthy. It is produced by taking the header and payload, running them through a cryptographic signing function using a secret key that only the server holds, and appending the result. The server does this at login when it issues the token.
Here is why tampering fails: if a user decodes the payload, changes their role from viewer to admin, and re-encodes it, the header and payload no longer match the original signature. When the server receives that modified token, it recomputes the signature from the header and payload it just received — and the result is completely different from the signature attached to the token. The server rejects it.
The attacker cannot simply recompute a valid signature because they do not have the server's secret key.
The key security property is this: the token's contents are visible to anyone, but they are bound to the signature. Change anything in the header or payload, and the signature breaks. Forge a valid signature without the secret key, and you cannot. The token is not confidential — it is tamper-evident.
Advantages of Stateless JWTs
No server-side storage. No session store to maintain, scale, or back up. No database lookups on every request. This simplifies your architecture considerably.
Horizontal scaling is trivial. Because no state is shared between servers, any instance can validate any token. Add servers arbitrarily, with no shared Redis cluster required.
Works across domains. JWTs are sent in the Authorization header, which is not domain-bound like cookies. This makes them natural for APIs called by multiple frontends — web, mobile, and third-party.
Self-contained information. The token carries the user ID and claims, eliminating the need to look up role or basic metadata on every request (though you should still verify that permissions haven't changed for sensitive operations).
Reduced database load. For systems where permissions rarely change, JWTs can meaningfully reduce database reads at scale.
Disadvantages of Stateless JWTs
Revocation is hard or impossible. This is the fundamental problem. A JWT is valid until it expires. There is no logout that truly invalidates a token. If a token is stolen, the attacker retains access until expiry. Every workaround — a revocation blacklist — involves storing state, which defeats the original purpose.
Token size is large. A session ID is 32 bytes. A JWT can be hundreds or thousands of bytes, especially with many claims. This overhead accumulates across millions of requests.
Password changes don't invalidate other sessions. When a user changes their password, all existing JWTs remain valid until they expire. The only reliable fix is a blacklist of tokens issued before the change — again, state.
Complex key management. Symmetric signing (HS256) means every server needs the same secret. Asymmetric signing (RS256) means managing key pairs and rotation schedules.
Algorithm confusion vulnerabilities. Poorly implemented JWT libraries can be tricked into accepting tokens signed with the none algorithm, or into confusing symmetric and asymmetric keys. These are well-documented, real-world vulnerabilities.
No built-in session visibility. Because the server stores nothing, listing "all devices where this user is logged in" requires implementing your own tracking — which is, once again, state.
When to Choose Stateless JWTs
Choose stateless JWTs when you need to scale horizontally without a shared session store. When you're building an API serving multiple frontends. When your access tokens are short-lived (minutes to hours) and you have a refresh token mechanism in place. When you can tolerate a delay between revocation and effect. Or when user permissions are stable for the duration of a session.
Part Four: The Great Misconceptions
Misconception 1: "Stateless means no state anywhere"
False. Stateless authentication means the authentication server stores no session state. Your system as a whole still has state: user accounts in your database, permissions records, JWT secrets or public keys, and any revocation blacklist or session tracking you add later. The question is never "does state exist?" It's "where is the state stored, and who manages it?"
Misconception 2: "Stateless scales infinitely; stateful doesn't"
False. Stateful authentication scales perfectly well — it just requires a shared session store that grows with you. Redis Cluster can handle millions of operations per second. Large companies including those operating at internet scale use stateful sessions extensively. The real difference is operational complexity, not theoretical scalability ceiling.
Misconception 3: "Stateless is more secure"
False. Security depends on implementation, not paradigm. Predictable session IDs, missing HttpOnly flags, and session fixation make stateful systems insecure. Algorithm confusion, weak secrets, and missing expiration make stateless systems insecure. Neither is inherently safer.
Misconception 4: "JWTs eliminate database lookups"
True but misleading. JWTs eliminate session lookups. For most requests you still need to fetch current permissions, account status, and other dynamic data from the database — unless you bake all of that into the token, which makes it large and creates synchronisation problems whenever the underlying data changes.
Misconception 5: "Stateless means I don't need to think about session management"
Dangerously false. With JWTs you still need to reason carefully about expiration times (too short degrades UX; too long is a security risk), refresh token rotation and storage, revocation strategies for compromised tokens, key rotation, and token size. Stateless authentication shifts complexity from the server to the client and to your operations team. It does not eliminate that complexity.
Part Five: The Hybrid Approach
Many production systems use a hybrid approach that takes the best of both paradigms.
Pattern 1: Short-Lived Access Tokens + Stateful Refresh Tokens
This is the most common hybrid pattern, used by OAuth 2.0 and OIDC.
Access tokens are JWTs with a lifetime of 5–15 minutes, stored client-side, and used to authorise API requests. They are not individually revocable, but their short lifespan limits the damage window.
Refresh tokens have a lifetime of days to months. They are stored server-side (stateful) and can be revoked instantly. Their sole purpose is to obtain new access tokens.
When the access token expires, the client sends the refresh token to a /refresh endpoint. The server validates it, checks it hasn't been revoked, and issues a new access token. Revoking a refresh token — on logout, password change, or suspicious activity — stops access at the next refresh cycle.
The result: You get the horizontal scalability of stateless access tokens with the revocation capability of stateful refresh tokens. The session store handles far fewer requests than it would in a pure stateful system, because it is only consulted at refresh time.
Pattern 2: JWT with a Server-Side Blacklist
For systems that need JWTs but also need revocation, you can maintain a blacklist of revoked token IDs using the jti (JWT ID) claim.
When a token needs to be revoked, its jti is added to a Redis set or database table. On every request, after validating the JWT signature, the server checks whether the jti appears in the blacklist. If it does, the request is rejected.
This works, but it reintroduces a server-side lookup on every request — the very thing JWTs were supposed to avoid. The blacklist is a state store, just smaller than a full session store because it only contains revoked tokens rather than all active sessions. Use this pattern only when you can't move to short-lived tokens and refresh token rotation.
Pattern 3: Sessions for Web, JWTs for APIs
Many mature applications use both: server-side sessions with cookies for the main web application, and JWTs for mobile apps and third-party API access. The same backend validates both.
Sessions give browser users revocability and simplicity. JWTs give API consumers portability and cross-domain compatibility. This is acceptable overhead when the API is genuinely separate from the web application.
Part Six: Decision Framework
The Direct Question to Ask First
Do we actually need stateless authentication?
If you cannot answer yes with a specific reason — extreme scale, cross-domain APIs, mobile-first architecture — then use sessions. They are simpler, give you immediate revocation, and you will almost certainly want that control later.
Decision Tree
Do you need immediate revocation (banking, healthcare, enterprise compliance)?
- Yes → Can you tolerate a shared session store?
- Yes → Use stateful sessions
- No (very high scale) → Use hybrid: short-lived JWTs + stateful refresh tokens
- No (social media, content site, lower-risk app) → Do you need cross-domain or mobile support?
- Yes → Use stateless JWTs
- No → Use stateful sessions (simpler, safer)
By Application Type
Traditional web app (Rails, Django, Laravel): Stateful sessions. This is what these frameworks are built for and what they do best.
Single-page app (React, Vue, Angular) with your own API: Either works. JWTs are popular, but sessions work equally well. Your actual requirements — not trend — should decide.
Public API used by third parties: Stateless JWTs, or OAuth 2.0 with opaque tokens for maximum revocation flexibility.
Mobile app with a backend: JWTs. Easier to store and send than cookies in a native context.
Banking or healthcare: Stateful sessions, short timeouts, MFA. Compliance and user safety require immediate revocability.
Microservices architecture: Hybrid. The API gateway validates tokens; internal services trust them for the request lifetime.
System with dynamic permissions: Stateful sessions, or very short-lived JWTs (minutes, not hours). Permissions that can change mid-session need a mechanism to enforce those changes promptly.
Part Seven: Common Pitfalls
Pitfall 1: Using JWTs When You Need Revocation
Symptoms: Your logout button doesn't truly log users out. Users change their password but remain authenticated on other devices. You cannot terminate a compromised session.
Fix: Switch to stateful sessions, or implement the hybrid pattern with short-lived access tokens and stateful refresh tokens.
Pitfall 2: Storing JWTs in localStorage
Symptoms: You're using localStorage for convenience without considering that any XSS vulnerability on your domain gives an attacker access to every token stored there.
Fix: Store JWTs in HttpOnly cookies wherever possible. If localStorage is unavoidable, implement a strict Content Security Policy to reduce XSS exposure. Understand that this mitigation is not a guarantee.
Pitfall 3: Overly Long JWT Expiration
Symptoms: Your JWTs expire in 7 days, 30 days, or never. A single stolen token gives an attacker an extended window of access.
Fix: Shorten access token expiration to 5–15 minutes. Use refresh tokens for long-lived sessions. The inconvenience is manageable; the security benefit is real.
Pitfall 4: No Plan for Session Store Failure
Symptoms: You run a single Redis instance. When it goes down, all authenticated requests fail and every user is effectively logged out.
Fix: Use a clustered Redis setup with failover. Implement graceful degradation — at a minimum, a read-only mode or stale session caching to keep users authenticated through brief outages.
Pitfall 5: Putting Too Much in the JWT Payload
Symptoms: Your JWT includes the user's full profile, complete permissions list, and audit trail. The token is several kilobytes. Every single request carries this overhead across the wire.
Fix: Keep JWTs small. Store only the user ID and the minimum claims required for routing decisions. Fetch dynamic data — roles, feature flags, account status — from a fast cache or the database when needed, not from the token.
Pitfall 6: Ignoring Token Theft Scenarios
Symptoms: You've chosen JWTs but haven't thought through what happens when one is stolen — through XSS, a compromised device, or a network interception.
Fix: Have an explicit incident response plan for token compromise. This means short expiration times, refresh token rotation (a new refresh token is issued with every refresh and the old one is invalidated), and anomaly detection on refresh patterns. Without these, a stolen long-lived JWT is an unrevokable skeleton key.
Part Eight: Real-World Examples
GitHub uses server-side sessions for github.com. Logging out invalidates your session immediately. Changing your password revokes all other sessions. For a platform storing sensitive source code, immediate revocability is non-negotiable.
Stripe uses API keys — a form of long-lived, stateful token — for their API. Each key is stored in Stripe's database and can be revoked instantly from the dashboard. The key itself is a random string referencing a server-side record. This is stateful authentication, regardless of how it looks on the surface.
Auth0, as an identity provider, issues JWTs by default but also provides a revocation endpoint that maintains a token blacklist. When you call the logout endpoint, Auth0 adds the token to a blacklist and subsequent requests check against it. This is the hybrid blacklist pattern.
Your bank most probably uses stateful sessions with short timeouts — typically 15 to 30 minutes of inactivity. Regulatory requirements and security standards demand immediate logout and revocation. A stolen JWT that remains valid for hours is not an acceptable risk profile for financial services.
Part Nine: Where This Fits in the Bigger Picture
The choice between stateful and stateless authentication determines how your backend validates identity on every single request.
The stateful flow:
The stateless flow:
Both attach a user identity to the request. But they fail differently.
A stateful failure — the session store is down — affects every authenticated request simultaneously. Users are logged out en masse until the store recovers. This is a single point of failure that must be engineered around.
A stateless failure — signature verification fails for a given token — rejects only that request. There is no external dependency to go down. But if your signing key is compromised, every token in circulation is compromised, and you have no way to selectively revoke them.
The choice also cascades into how you handle authorisation. With stateful sessions, permissions can be updated server-side and take effect on the next request. With stateless JWTs, permissions are baked into the token until it expires — making real-time permission changes either impossible or dependent on a hybrid mechanism.
Conclusion: The Right Tool for the Job
A session is like a key to your house. You give it to someone, and they can come and go. If they lose the key, you change the lock. Access is revoked immediately.
A JWT is like a prepaid concert ticket. The ticket contains all the information — seat number, date, time. The venue doesn't keep a list of who has tickets. They check the signature and let you in. If your ticket is stolen, the thief can attend the concert. You cannot cancel the ticket. You wait for the concert to end.
Keys are the right tool for your house. Tickets are the right tool for a stadium with 50,000 attendees.
JWTs are genuinely valuable for distributed APIs, mobile applications, and systems that span multiple domains and organisations. But they are not a default upgrade from sessions. They are a different tool with a different set of trade-offs, and adopting them without understanding those trade-offs is how you end up spending $2 million to undo a decision that seemed obvious at the time.
Before you write your first line of authentication code, ask the question :
Do we actually need stateless authentication?
If you can answer that with a clear yes — and a specific reason — then JWTs may well be right for you. If the answer is "because everyone's using them" or "because they scale," go back to the trade-off matrix. Sessions scale too. And they give you something JWTs cannot: the ability to say "you're done" and mean it immediately.
About N Sharma
Lead Architect at StackAndSystemN Sharma is a technologist with over 28 years of experience in software engineering, system architecture, and technology consulting. He holds a Bachelor’s degree in Engineering, a DBF, and an MBA. His work focuses on research-driven technology education—explaining software architecture, system design, and development practices through structured tutorials designed to help engineers build reliable, scalable systems.
Disclaimer
This article is for educational purposes only. Assistance from AI-powered generative tools was taken to format and improve language flow. While we strive for accuracy, this content may contain errors or omissions and should be independently verified.
