Learning Paths
Last Updated: April 9, 2026 at 10:30
RSA vs ECC: Which Asymmetric Algorithm Should You Use?
Key sizes, performance trade-offs, and how to choose between RSA and ECC for TLS certificates, SSH keys, and JWTs
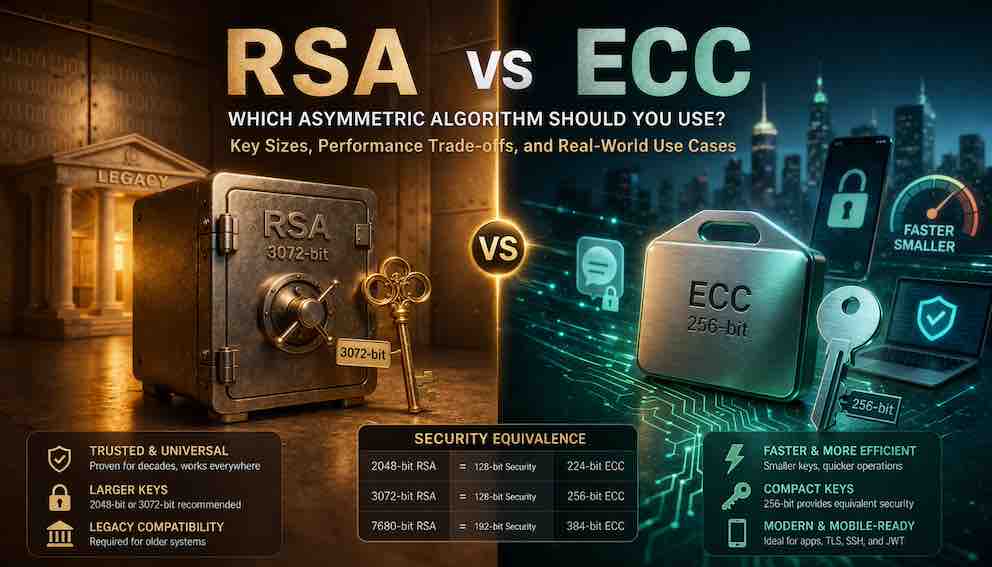
Choosing between RSA and ECC is one of the most important decisions in public-key cryptography, affecting everything from TLS handshake speed to JWT token size. RSA has been the gold standard since the 1970s, offering unmatched compatibility with legacy systems but requiring large 2,048-bit or 3,072-bit keys. ECC achieves the same security with much smaller 256-bit keys, making it faster, more efficient, and better suited for mobile devices, high-traffic servers, and modern applications. This article breaks down the security equivalence, performance trade-offs, and real-world scenarios to help you decide whether RSA, ECC, or both is right for your TLS certificates, SSH keys, and JWT signatures.
The Cast-Iron Safe and the Titanium Lockbox
Imagine you need to protect something valuable and you have two containers to choose from.
The first is a cast-iron safe. Massive, heavy, and built like a fortress. Banks have trusted it for over a century. It has never been cracked. But it is heavy. Moving it requires effort. It takes up space. The key is enormous.
The second is a titanium lockbox. Small, light, modern. It provides the same protection as the cast-iron safe — no attacker can break into either — but it uses advanced materials and clever engineering to get there with less weight, less space, and a much smaller key. It is newer, so not every bank accepts it. But where it is accepted, it is simply better.
This is RSA and ECC.
RSA is the cast-iron safe. It has been the standard for asymmetric cryptography since the 1970s. It is everywhere. Every system supports it. But its keys are large — 2,048 bits or more — and operations are slower.
ECC is the titanium lockbox. It achieves equivalent security with much smaller keys. A 256-bit ECC key provides the same protection as a 3,072-bit RSA key. It is faster, more efficient, and uses less power. But it is newer, and some legacy systems do not support it.
Both are secure. Both are widely used. But one may be better suited to your specific situation. This article helps you decide which.
A Quick Refresher on Asymmetric Encryption
Before comparing the two algorithms, a brief reminder of how asymmetric encryption works. It uses a key pair: a public key that can be shared freely, and a private key that must remain secret.
The two keys have different jobs — and it helps to see each one grounded in something real.
Encryption for secrecy. Anyone with your public key can encrypt a message. Only you, with your private key, can decrypt it. When you visit a website over HTTPS, encryption is what ensures that no one between you and the server can read the data being exchanged — not your ISP, not someone on the same Wi-Fi network, nobody.
Signing for identity. You sign data with your private key. Anyone with your public key can verify that signature, confirming the data came from you and has not been tampered with. When a server issues a JWT (JSON Web Token) after you log in, it signs that token with its private key. Every time your browser sends the token back with a request, the server verifies the signature — confirming the token is genuine and has not been altered.
Both jobs exist because they solve different problems. Encryption keeps secrets. Signing proves authenticity. You will encounter both throughout your career as a developer.
RSA and ECC both support encryption and signing, but they achieve this through very different mathematics, with very different trade-offs.
Takeaway: Encryption hides data in transit. Signing proves who created something and that it has not changed. RSA and ECC can both do either job.
RSA: The Old Reliable
RSA is named after its creators — Rivest, Shamir, and Adleman — who published the algorithm in 1977. Its security rests on the mathematical difficulty of factoring large prime numbers. Multiplying two large primes together is easy. Working backwards to figure out which two primes were multiplied is, for large enough numbers, computationally infeasible with today's technology.
Common RSA key sizes:
- 1,024 bits — broken, do not use under any circumstances
- 2,048 bits — minimum acceptable today
- 3,072 bits — recommended for new systems
- 4,096 bits — high security, but carries a meaningful performance cost
What makes RSA slow. RSA operations require working with very large numbers — 2,048 bits or more. Key generation is particularly expensive; on constrained devices it can take several seconds. Signing and verification are faster, but still significantly slower than ECC at equivalent security levels.
Where you find RSA. TLS certificates (still the most common type, though ECC is growing rapidly), JWT signatures using RS256, SSH keys on older systems, PGP/GPG email encryption, code signing certificates, and legacy VPN protocols.
Why RSA remains everywhere. One word: compatibility. RSA has been around for nearly 50 years. Every system that supports asymmetric cryptography supports RSA. If you need to work with older infrastructure, government systems, or anything not recently updated, RSA is the safe choice.
Takeaway: RSA is the most compatible asymmetric algorithm. When legacy support is uncertain, RSA works. Use at least 2,048 bits; 3,072 is better for anything new.
ECC: The Modern Efficient
ECC stands for Elliptic Curve Cryptography. Rather than relying on prime factoring, it is based on the mathematics of elliptic curves — a different branch of number theory entirely.
You do not need to understand the mathematics to use ECC effectively. What matters is this: ECC relies on a mathematical problem that is even harder to reverse than the factoring problem that secures RSA. Because the underlying problem is harder, ECC can use much smaller keys to achieve the same level of protection. That size difference compounds into real, practical gains everywhere keys are used.
Common ECC key sizes and their RSA equivalents:
- 224 bits ≈ 2,048-bit RSA (acceptable for most applications)
- 256 bits ≈ 3,072-bit RSA (standard recommendation)
- 384 bits ≈ 7,680-bit RSA (high security, long-term protection)
- 521 bits ≈ 15,360-bit RSA (extreme security, overkill for most uses)
A 256-bit ECC key is 12 times smaller than a 3,072-bit RSA key providing equivalent protection. Smaller keys mean faster handshakes, smaller certificates, smaller tokens, less memory, and less bandwidth — at every point in your system where keys are transmitted or stored.
Curve choice: what you actually need to know. ECC is not a single algorithm — it is a family of algorithms based on different curves. There are many curves in existence, but in practice you only need two safe defaults to get started.
P-256 (also called secp256r1) is the curve standardised by the US government and supported by virtually every modern system. It is the right choice when you need broad compatibility.
Ed25519 is a more modern curve designed by cryptographer Daniel Bernstein. It is faster, easier to implement correctly, and has no concerns about how its parameters were chosen. It is specifically designed for digital signatures. For SSH keys and new signing use cases, Ed25519 is the preferred choice today.
There are other curves — P-384, P-521, secp256k1 (used by Bitcoin) — but you can set those aside until you encounter a specific need for them. Start with P-256 for general use and Ed25519 for signatures.
Where you find ECC. Modern TLS certificates (growing rapidly for high-traffic sites), JWT signatures using ES256 or EdDSA, SSH keys (Ed25519 is now the recommended default), the Signal Protocol and other modern messaging systems, blockchain applications, and mobile devices where efficiency is critical.
Takeaway: ECC gives you the same security as RSA with much smaller keys. For new systems, use P-256 for general compatibility and Ed25519 for signatures. You do not need to understand the curve mathematics to use them safely.
Performance: Speed Matters at Scale
Before looking at the numbers, it helps to understand which operations happen most often in a real system. In most applications, verification happens far more often than signing. A JWT is signed once when a user logs in, but verified on every API request that user makes — potentially thousands of times. A TLS certificate is signed once by a certificate authority, but verified millions of times by browsers. Keeping this in mind helps you interpret performance comparisons correctly.
Key generation. Generating an RSA key pair is slow — often several seconds on constrained hardware. Generating an ECC key pair takes milliseconds. If your system generates many key pairs (per-user keys, ephemeral session keys), ECC is dramatically better.
Signing. RSA signing is slower than ECC signing at equivalent security levels. For high-throughput systems — a JWT issuer handling millions of tokens per hour, or a certificate authority signing certificates at scale — ECC can handle significantly more operations per second.
Verification. This is the one area where RSA holds an edge. RSA uses a small public exponent (typically the number 65537), which makes verification fast. ECC verification involves more complex curve arithmetic. At very high verification volumes, RSA may perform better. In practice, the gap is rarely large enough to change a real-world decision.
TLS handshake. ECC wins clearly. Smaller keys mean less data to transmit during the handshake, and ECDHE (Elliptic Curve Diffie-Hellman Ephemeral) key exchange is faster than its RSA-based equivalent. A server handling millions of TLS connections per day sees meaningful throughput gains from switching to ECC certificates.
Takeaway: ECC is faster for signing and key generation. RSA may be slightly faster for verification at very high volumes, but this rarely changes real-world decisions. For most systems, ECC wins on overall performance.
Perfect Forward Secrecy: Why ECC Matters for TLS
This concept explains one of the biggest practical reasons ECC has become dominant in modern TLS. You may have seen the term "Perfect Forward Secrecy" (PFS) in security audits or server configuration guides — here is what it actually means.
In older TLS configurations using RSA key exchange, the server's long-term private key was used directly to help establish each session's encryption keys. The consequence: if an attacker recorded your encrypted traffic and later obtained the server's private key — through a breach, a court order, or anything else — they could go back and decrypt all previously recorded sessions. Past conversations were not safe.
ECDHE (Elliptic Curve Diffie-Hellman Ephemeral) solves this. A fresh, temporary key pair is generated for each TLS session. Once the session ends, those temporary keys are discarded permanently. Even if the server's long-term private key is compromised years later, past sessions cannot be decrypted, because the keys that protected them no longer exist anywhere.
ECC makes ECDHE fast enough to use on every single connection at scale. This is why modern TLS configurations strongly prefer ECDHE cipher suites, and it is a core reason ECC certificates are now preferred over RSA for web servers.
Takeaway: Perfect Forward Secrecy means past sessions stay private even if your server's private key is stolen in the future. ECDHE is the standard way to achieve this in TLS today, and it requires ECC.
A Critical Security Note: The ECDSA Nonce Problem
ECC used for signatures — ECDSA specifically — has one vulnerability that every developer should understand before using it in production.
Think of the nonce as a one-time code used internally during the signing process. Each time you sign something, ECDSA generates a random nonce and incorporates it into the calculation. This nonce must be unique for every single signature your system ever produces. If the same nonce is accidentally used twice — even once across your entire system's lifetime — an attacker who collects both signatures can mathematically recover your private key. Not weaken it. Recover it entirely.
This is not theoretical. In 2010, Sony's PlayStation 3 was compromised because Sony reused the same nonce for every ECDSA signature they produced. Researchers obtained two signatures, observed the repeated nonce, and derived Sony's private key. Every piece of software Sony had ever signed was now forgeable.
Ed25519 eliminates this risk by design. Instead of relying on a random nonce, Ed25519 derives the nonce deterministically from the message and the private key using a hash function. The result is always unique without depending on a random number generator at signing time. This makes Ed25519 significantly harder to misuse, which is one of the main reasons it is the preferred algorithm for new signing use cases.
If you use ECDSA (for example, with P-256), verify that your library uses a cryptographically secure random number generator. Better still, use Ed25519 for signatures wherever your environment supports it.
Takeaway: ECDSA requires a unique random number (nonce) per signature. Reusing it even once exposes your entire private key. Ed25519 avoids this problem entirely through deterministic signing, making it the safer default for new signature use cases.
Security Considerations for Both Algorithms
Both RSA and ECC are considered secure when used correctly. Each has specific failure modes worth knowing.
RSA security considerations:
Key size matters absolutely. Do not use 1,024-bit RSA — it is broken. Use 2,048 bits as a minimum. For systems that need to remain secure beyond 2030, use 3,072 bits.
Padding is critical. Here is why padding is needed.
RSA has a dangerous property: it is deterministic. The same message encrypted with the same public key always produces the same ciphertext. This sounds harmless, but it creates real vulnerabilities.
Imagine an attacker sees an encrypted message traveling across the network. Without padding, they could guess what the plaintext might be — say, "yes" or "no" — encrypt those guesses using the public key, and compare the results to the captured ciphertext. If a guess matches, they have broken the encryption.
Worse, RSA without padding has mathematical properties that attackers can exploit to decrypt messages without ever knowing the private key.
Padding solves this by adding random data to your message before encryption. The same message encrypted twice will look completely different each time because the random padding changes. This makes guessing attacks impossible.
Modern RSA uses OAEP (Optimal Asymmetric Encryption Padding) for encryption and PSS (Probabilistic Signature Scheme) for signatures. These padding schemes are designed to be secure. Most libraries default to them, but it is worth verifying.
Side-channel attacks are real. RSA implementations can leak private key information through timing variations. An attacker measuring how long a decryption takes can slowly reconstruct your private key.
Use well-maintained, audited libraries rather than implementing RSA yourself.
ECC security considerations:
Curve choice matters. Stick to the safe defaults: P-256 for general use, Ed25519 for signatures. Never use a curve from an obscure or unreviewed source, and never implement elliptic curve arithmetic from scratch.
Random number quality is critical for ECDSA. As described above, poor randomness in nonce generation has broken real systems. Ed25519's deterministic signing removes this dependency entirely.
The concern both algorithms share — quantum computers:
Both RSA and ECC are vulnerable to Shor's algorithm, which would allow a sufficiently powerful quantum computer to break either. This is a long-term concern, not an immediate threat. No quantum computer capable of breaking 2,048-bit RSA or 256-bit ECC exists today or is expected imminently. For data that must remain confidential for 15 or more years, begin evaluating post-quantum options now. For everything else, RSA and ECC remain the right choices.
Takeaway: Both algorithms are secure when used correctly. The most common real-world failures come from wrong key sizes, outdated padding, and poor random number generation — not from the algorithms themselves being broken.
Post-Quantum Cryptography: What You Should Know in 2026
RSA and ECC will eventually need to be replaced as quantum computing matures. NIST completed its standardisation process in August 2024, finalising three post-quantum algorithms. These names are important for awareness, but you do not need to use them today unless you are working on systems with very long time horizons or handling highly sensitive data.
ML-KEM (FIPS 203) handles key exchange, replacing ECDH and RSA key exchange in TLS.
ML-DSA (FIPS 204) handles digital signatures, replacing ECDSA and RSA signatures.
SLH-DSA (FIPS 205) is a more conservative hash-based signature alternative.
For most production systems in 2026, RSA and ECC are still the correct choices. However, if you are designing a system that must remain secure for 15 or more years, or if you work in defence, healthcare, or financial infrastructure, start your post-quantum planning now. Some organisations are already deploying hybrid certificates that combine classical ECC with a post-quantum algorithm, maintaining compatibility while adding quantum resistance.
Takeaway: Post-quantum standards are finalised but not yet widely deployed. Know they exist. For most systems today, ECC and RSA are the right tools.
The Also-Rans: Other Asymmetric Algorithms
You may occasionally encounter these older algorithms. They are worth recognising so you can confidently move past them.
DSA (Digital Signature Algorithm) is an older US government standard designed only for signatures. Slower than ECC, no advantages over it, and rarely seen in new systems. Avoid.
ElGamal is an asymmetric encryption algorithm that predates widespread ECC use. Not commonly seen outside academic contexts today. ECC-based approaches have superseded it.
Textbook RSA (RSA with no padding scheme) is fundamentally insecure and should never appear in real code. If you see an RSA implementation that does not explicitly mention OAEP or PSS, treat it as broken.
In 2026, the only classical asymmetric algorithms you should reach for in new systems are RSA (2,048 bits or larger, with proper padding) and ECC (using P-256 or Ed25519). Everything else is legacy or experimental.
How to Choose: A Decision Framework
Use ECC (Ed25519 or NIST P-256) when:
- You are building a new system with no legacy constraints
- Performance and efficiency matter — mobile, IoT, high-traffic servers
- You want smaller certificates, smaller JWTs, or smaller keys
- You are generating many key pairs (per-user, per-session, ephemeral)
- You are setting up SSH keys for your team
- You need Perfect Forward Secrecy in TLS
Use RSA (2,048 bits or larger) when:
- You need compatibility with older systems that do not support ECC
- You are operating under regulations that explicitly mandate RSA
- You are integrating with a legacy system that only accepts RSA certificates or tokens
Support both when:
- You are building a public-facing service that must work for all clients
- You want ECC efficiency for modern clients while maintaining RSA fallback for legacy systems
In TLS, modern servers can present an ECC certificate by default while still accepting RSA connections from older clients. Some organisations run dual certificate stacks for exactly this reason. For JWT signing, you can issue new tokens with ES256 (ECC) while continuing to accept RS256 (RSA) tokens from older integrations during a migration.
Takeaway: When building something new, default to ECC. Use RSA only when a legacy or regulatory constraint requires it. Support both if your audience includes a mix of old and new clients.
RSA and ECC in the Security Stack
RSA and ECC appear at multiple layers of a typical application. Seeing where they fit makes the earlier concepts more concrete.
In TLS certificates (authentication). Your browser connects to a server. The server presents a certificate containing its public key — either RSA or ECC. Your browser uses that key to verify the certificate chain and participate in key exchange. ECC certificates with ECDHE provide both speed and Perfect Forward Secrecy.
In JWTs (authorisation). After you log in, the server signs a JWT with its private key. Every subsequent request includes that token. The server (or a separate verification service) checks the signature with the corresponding public key. The algorithm is declared in the JWT header: RS256/RS384 use RSA; ES256/ES384/ES512 use ECDSA; EdDSA uses Ed25519.
In SSH (authentication). Your machine holds a private key — RSA or Ed25519. The server stores your public key. When you connect, SSH proves you possess the private key by producing a digital signature without ever transmitting the key itself. Ed25519 is the modern default.
In code signing (integrity). Software publishers sign executables with a private key. Your operating system or package manager verifies the signature before running or installing the software. This is what prevents someone from slipping a malicious binary into a legitimate software update.
What to Take Away
RSA and ECC are the two dominant asymmetric algorithms. RSA is older, larger, slower, and more compatible. ECC is newer, smaller, faster, and more efficient.
After reading this article, you should be able to:
- Explain the difference between encryption (for secrecy) and signing (for authenticity), with real examples from HTTPS and JWTs
- Understand key size equivalents — 256-bit ECC provides protection equivalent to 3,072-bit RSA
- Know that ECC is faster for key generation and signing; RSA verification holds a slight edge at very high volumes
- Understand why ECDSA nonce reuse is catastrophic, and why Ed25519 eliminates this risk through deterministic signing
- Know that ECDHE enables Perfect Forward Secrecy in TLS — protecting past sessions even if your private key is later compromised
- Choose ECC (P-256 or Ed25519) for new systems without legacy constraints
- Choose RSA when compatibility with older systems or regulations requires it
- Avoid 1,024-bit RSA, untrusted ECC curves, PKCS#1 v1.5 padding, and ECDSA nonce reuse
- Use Ed25519 for SSH keys, ES256 or EdDSA for JWT signatures, and ECC with ECDHE for TLS
- Know that post-quantum standards (ML-KEM, ML-DSA) are finalised and adoption is beginning, though RSA and ECC remain the right choice for most production systems today
And most importantly: the algorithm is only one part of security. Key size, padding, random number quality, and correct implementation matter as much as the algorithm you choose. A correctly chosen algorithm used incorrectly is not secure.
The Cast-Iron Safe and the Titanium Lockbox, Revisited
The cast-iron safe — RSA — has been protecting valuables for generations. It is trusted. It is everywhere. If you work with systems that only accept cast-iron safes, you use RSA.
The titanium lockbox — ECC — provides the same protection with less weight, less space, and faster access. It is the modern choice. If you are building something new with no legacy constraints, this is simply better.
Both keep your valuables safe. Neither is a mistake. But one is better suited to your specific situation.
Choose accordingly.
About N Sharma
Lead Architect at StackAndSystemN Sharma is a technologist with over 28 years of experience in software engineering, system architecture, and technology consulting. He holds a Bachelor’s degree in Engineering, a DBF, and an MBA. His work focuses on research-driven technology education—explaining software architecture, system design, and development practices through structured tutorials designed to help engineers build reliable, scalable systems.
Disclaimer
This article is for educational purposes only. Assistance from AI-powered generative tools was taken to format and improve language flow. While we strive for accuracy, this content may contain errors or omissions and should be independently verified.
